When Quantum Meets AI: Preparing for the Next Shift in Cybersecurity
In our previous article, we explored how quantum computing could eventually undermine today’s encryption methods. There is, however, another layer to this discussion that deserves closer attention — the accelerating role of artificial intelligence (AI) and what may happen when AI and quantum computing begin to reinforce each other. This is where the conversation shifts […]
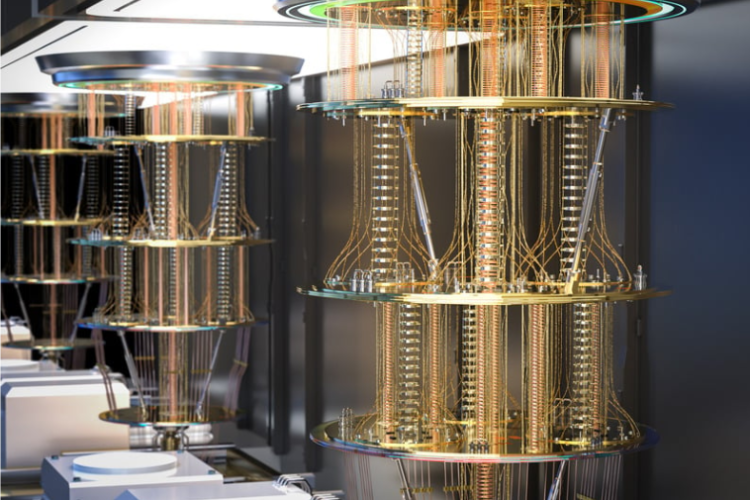
Quantum Computing Is Coming: What It Means for Encryption and Cybersecurity
Hello! We hope you’re doing well. From time to time, we come across articles that don’t just talk about today’s cyber risks, but about what may fundamentally change cybersecurity in the years ahead. One topic that continues to surface in those discussions is quantum computing — and what it could mean for encryption, data protection, […]
Why Information Sharing Matters in Cybersecurity — and Why It’s Still Not Easy
One topic that comes up regularly in conversations with clients and peers is information sharing — the idea that organisations can better defend themselves by sharing what they’re seeing, learning, and experiencing during cyber incidents. In theory, information sharing sounds straightforward. In practice, it’s complicated, imperfect, and sometimes frustrating. Yet despite the challenges, it remains […]
When Compliance Takes Over: A Conversation Many Businesses Are Afraid to Have
One of our favourite parts of working with clients is spending time talking about their real challenges — not just technology, but priorities, pressures, and what genuinely gets in the way of doing good work. These conversations are often insightful, sometimes uncomfortable, and almost always valuable. One topic that comes up repeatedly, particularly in accounting, […]
Apple, Privacy, and Competition: What a €98.6 Million Fine Tells Us About Data Protection
Today, we’d like to share a story that sits at the intersection of privacy, regulation, and business impact — and it’s a good example of how even well-intentioned security and privacy controls can raise complex questions. Recently, Apple was fined €98.6 million by Italy’s competition authority, which ruled that one of Apple’s privacy features unfairly […]
Why the Biggest Cyber Threat in 2026 Isn’t a Hack — It’s Trust
Recently, we came across a thought-provoking article about how cyber attacks are changing as we move into 2026. What stood out wasn’t a new software vulnerability or a complex technical exploit — it was the idea that the most successful breaches are now more likely to exploit trust than technology. With artificial intelligence advancing rapidly, […]
Social Media and Messaging Apps: Simple Security Lessons for Everyday Use
Social media and messaging apps have become part of our daily routine — we check them in the morning, use them for work conversations, and scroll through them at night. Recently, we were reading some guidance on social media security and thought it was worth sharing, because it highlights something many people don’t realise: the […]
What We Can Learn from the Endesa Data Breach
Today, we’d like to share a recent cybersecurity incident that caught our attention — not because it involved sophisticated hacking techniques, but because it highlights how customer data can still be exposed even when core systems remain operational. It’s a useful case study for any organisation that handles personal or payment information. Spanish energy company […]
A New Phishing Technique Using Legitimate Hosting — What Businesses Should Know
Hello and welcome! We hope you’re doing well. Today, we’d like to share an interesting cybersecurity article we came across that highlights how phishing tactics are continuing to evolve. What stood out to us is not just who is behind the attack, but how it was carried out — by abusing legitimate online services that […]
Digital Wallets and Decentralised Identity Are Accelerating
According to digital identity specialists at Ping Identity, the coming year will see rapid growth in digital wallets, decentralised identity, and continuous monitoring of both human and machine identities, driven largely by the rise of AI-enabled cyber threats. Below is our summary and interpretation of the key themes from the article by Shannon Williams, journalist […]