What is malware?
Malware is a various type of malicious software, developed
by the cybercriminals (called hackers) to allow them steal sensitive data,
damage or destroy computers and computer systems. The common malware that the
hackers usually hack into computers are viruses, worms, Trojan viruses,
rootkits, spyware, and ransomware.
The malware can install to your device either by downloaded
infected file or installed infected software or download link in an email which
automatically installs malicious software onto your device called Phishing and
Spear-phishing.
The example of malware intentionally:
- Gathering intelligence and infiltrating
Unauthorized extraction of data,
including emails, plans, and particularly confidential details like passwords.
- Causing chaos and demanding payment
By encrypting networks and PCs,
rendering them inoperable. When this is done with the intention of financial
extortion, it’s termed ransomware.
- Sabotage or malicious defacement
Deliberately ruining computer
systems to harm your network infrastructure.
- Misappropriating computing resources
Utilizing your computational power
for activities such as running botnets, engaging in crypto mining, or sending spam
emails.
- Financial profit
Selling your organization’s intellectual
information on the dark web.
Types of malwares
- Virus
It’s a harmful program that has been linked to a file or
document. Once the file is downloaded, opened, and activated, it can propagate
from one device to another. Viruses have the potential to cause disruptions to
the operating system, leading to issues like data loss.
- Worms
It spreads through a network by replicating itself at an
exponential rate once the file is downloaded or connected to the network. The effect of worms can cause the data loss
and operational disruption on a device like viruses.
- Trojan virus
It designed to gain access to sensitive data and then
modify, block, or delete data once the user downloads file or software.
- Rootkits
It is a malware that designed to grant the hacker
administrative rights to a targeted computer. It is difficult to detect or
remove because it is installed manually outside of the typical layer of user
applications.
- Spyware
It is a software that designed to track the user’s internet
activities and application used activities, collect the credentials data such
as financial data, credit card information, username, and password. Then send
the data to the hacker without user’s permission. This malware is mostly used
to steal financial information and personal information. The keylogger is
mostly used to steal username and password information.
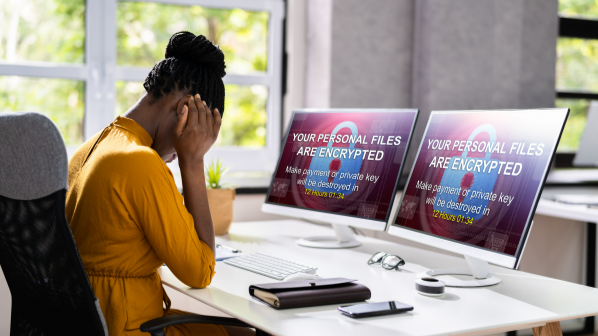
- Ransomware
It is a type of malware that the hacker uses to block users
access to a system or credential information by encrypted it and threat them to
pay money to decrypted and release accessibility to the users. There are two
different types of ransomware, one is called crypto ransomware which targets to
encrypt files on a user’s device, another is locker ransomware which targets to
lock the users out of their device.